QAD EQMS
Enterprise Quality Management System
QAD EQMS meets IATF, ISO, and MMOG/LE Standards
Are your quality practices EMBEDDED in your manufacturing operations? Are you seeing high return rates, low customer satisfaction scores, loss of market share?
What about your SUPPLIERS’ QUALITY? How is their quality or delivery impacting your performance? Scrap, returns, complaints, lost revenue?
Do you know the full extent of your HIDDEN COST of quality? How much is it costing your business? What are the hidden costs buried in accepted overhead—expediting, rework teams and floorspace, replanning?
It’s estimated that the hidden cost of quality equates to roughly 15-20% of your total cost of goods sold. This translates to a potential direct hit to your EBITDA of 30% or more.
What if you had a solution to help you prevent these issues, to have as much control and visibility into your suppliers’ quality as you do your own, and to allow you to uncover, control and reduce those hidden costs of quality?
QAD EQMS is a fully integrated solution that empowers your entire organization to solve each of these problems.
New Product Introduction

Knowing a supplier's performance, with both real-time and historical data, is essential when awarding business to a new or existing supplier. Tying supplier awards to NPI projects and PPAP submissions reduces the risks associated with onboarding a new supplier or product and ensures smooth customer product launches. QAD EQMS streamlines the supplier management process and allows suppliers to interact directly within the system, increasing collaboration and communication.
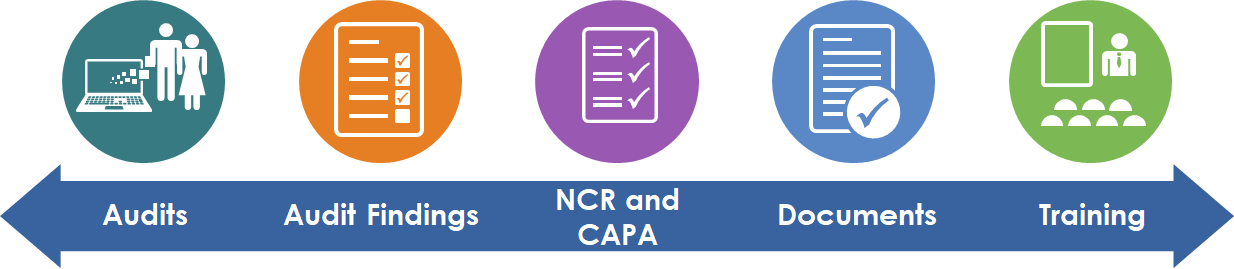
Document Control and Training Compliance
Documents and training are the backbone of your organization. They help establish best practices and ensure your business continues to grow and perform effectively. Poor documentation with manual training places your business at risk, especially with an ever-changing workforce. Remove this danger with an integrated document control and training management system.
Product and Process Change Management
Integrating your inspection process directly with your control plans ensures inspection requirements stay connected during change management. Coupled with automated non-conformance creation based on inspection failures results in reductions in the cost, time and complexity of change management.
Efficient Audit Processes
Regulated organizations must implement effective internal audit programs to drive compliance and continual improvement. Gain the maximum benefit from your audits with a closed-loop system to address product, process or system audits, plus manage any findings or non-conformities that may result in necessary procedure updates and re-training.
Process Change Management

Change is hard to manage and can result in unforeseen consequences that add risk to your company’s performance. Maximize your chances for success and reduce opportunities for failure by using standard methods for change requests, risk management, assessments, approvals and implementation through effective training.
Manage Risk
Businesses can incur a high cost when it comes to product defects and an even higher cost with product lawsuits. For some regulated industries, product defects and complaints can result in forced business shut down or even criminal action. A closed-loop, integrated system moves your organization from a reactive, costly business model to a culture of prevention with mitigated risks.
Continuous Improvement
Businesses must evolve to stay alive and continuous improvement is the tool to enable your teams to pause, reflect and make effective improvements happen. Maximize your ROI with an enterprise-level QMS that allows you to identify opportunities for improvement and effectively manage the tasks and resources needed to implement those ideas while constantly learning from the process.
Improve Visibility into Calibration Failures
Calibration failures expose organizations to excessive risk. What was tested? Has the product been released? What has to happen to prevent this? Gauge management fully integrated with NCR/CAPA and traceability puts the answers at your fingertips.
Controlling Supplier Deviations
Things change. How do you effectively manage the supplier deviations? A supplier’s inability to meet your exact requirements sometimes means deviations must be granted. An integrated system allows you to manage the supplier process end-to-end and ensures only the product meeting your agreed needs is delivered for use.
Supplier Quality Development
How you manage complaints or inspection failures will impact your financial performance. Improve your results with an integrated non-conformance and corrective action system with full linkage to supplier management. Effectively reduce the costs of poor quality and recoup the expenses for issues created by the supply base.
Thank you for reaching out to QAD! Your inquiry has been forwarded to the appropriate representative who will contact you shortly.
In the meantime, for more information on how we can work together toward building an Adaptive Enterprise please subscribe to the QAD Blog for commentary on the latest news and announcements from QAD and the industry.
If you would like to change your message settings, visit our Subscription Preference Center.